CCTV footage used in court
TDLR: CCTV is highly prevalent, and there are both direct and indirect ways in which it is used by authorities that you should be aware of.
Introduction
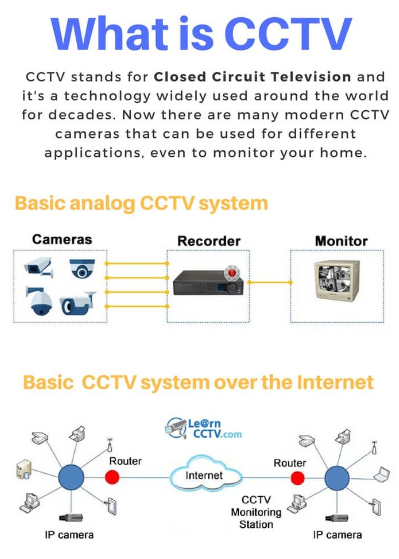
As we have previously discussed, technology is widely used by states as a means of maintaining control over populations. In some cases, it is explicitly designed for that purpose. This is particularly true of CCTV systems commonly found in public spaces and buildings. While there are certain methods to reduce exposure to CCTV surveillance, many people underestimate its potential consequences. In this article, we will examine cases in which CCTV footage contributed to criminal convictions and analyze how such outcomes might have been avoided.
How is CCTV used in court
The objective of this blog post is to show how CCTV is used as evidence in court and, especially, how it can be used against you.
First, I would like to provide some information about the rules that have been established to allow CCTV footage to be accepted as evidence in court.
The main concept to understand here is the chain of custody. "The chain of custody refers to the chronological documentation and handling of evidence, ensuring that from the time evidence is collected until it is presented in court, there has been no tampering, alteration, or substitution."
Basically, this means that these rules were established to ensure that the footage used against you has not been altered in any way. However, in reality, there is no absolute guarantee. Let's take a closer look at what is required and explore why it may not be entirely secure for you:
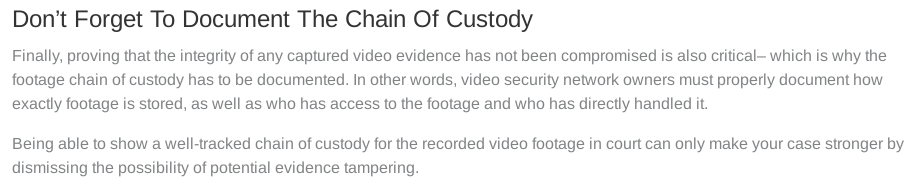
1) Who retrieved the footage
This point is not particularly complex. Since you and your lawyer should be able to review the footage in court, you must be able to verify that it was indeed retrieved by the person listed in the chain of custody. The main challenge is that, if there has been any manipulation at this stage, proving it can be extremely difficult.
2) How it was retrieved
Here, it becomes more challenging to determine whether the information is accurate. Since setting up CCTV is relatively easy and involves a wide variety of technologies, detecting manipulation during a court case requires extensive technical knowledge.
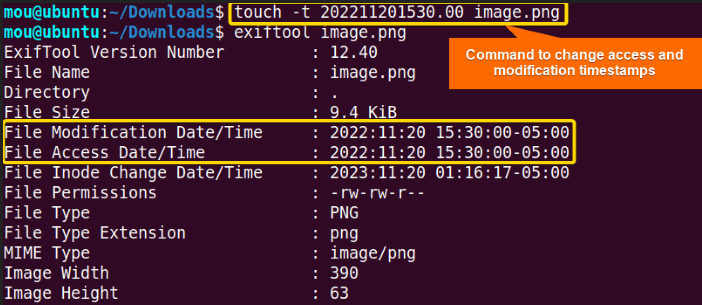
3) When and from where it was collected.
Here is where the real issue begins. Since metadata can be easily altered, the footage itself can also be manipulated. Videos metadata can be edited to suggest that you were at a particular location, even when you were not.
4) How it was stored.
Here, the same issue applies. This information can be manipulated, and in most cases, the court relies on official declarations. Additionally, there is no real guarantee that the storage is properly secured. As we know, governments can be lax in their OPSEC, so the footage could have been altered by external parties.
5) Who had access to it at different stages.
Here, two types of information can be used to track who accessed the footage you are reviewing. The first is the declared list of access provided by the authorities. The second consists of system logs, which should be available in any properly managed system.
However, both of these can be subject to manipulation. Since the rules primarily focus on the footage itself rather than the integrity of the associated logs, it becomes difficult to fully verify whether the footage has remained unaltered.
6) Whether it was sealed, cloned, or copied in a legally compliant manner.
The key point to focus on here is the notion of a “legally compliant manner.” This essentially means that the same institution seeking to use the CCTV footage against you is also responsible for determining how it is sealed, copied, or preserved.
As a result, you have very limited control over this process and are largely dependent on procedures managed by the opposing party. That's not exactly something fair...
Cases examples
To illustrate the potential impact of CCTV on individuals' lives, we will examine cases in which people were identified and arrested for sensitive or illegal activities as a result of CCTV surveillance.
Jesse Shane Kempson
In 2018, in Auckland, Grace Millane, a British tourist, was murdered by a man she had met online, Jesse Shane Kempson. CCTV footage showed the two together in the city center and later captured Kempson handling a suitcase. Grace Millane's body was later found inside that suitcase.
In this case, CCTV evidence played a crucial role for two main reasons. First, it established that the victim and Kempson were together shortly before her disappearance and showed him transporting the suitcase. Second, it helped investigators challenge inconsistencies in the defense's narrative by reconstructing movements and timelines.
You can find the court documents here that are showing that CCTV footages were used in court.

Jesse Shane Kempson was sentenced to life imprisonment.
This illustrates a key aspect of CCTV evidence: it does not necessarily need to capture a person committing an illegal act directly. It can be sufficient to place someone at a specific location, demonstrate movements, or contradict statements. In many cases, surveillance footage is used to build a timeline, confirm associations, and expose discrepancies rather than to show the act itself.
Mohammed Adam
In 2016, in Ghana, a man named Mohamed Adam was captured on CCTV entering a warehouse through the roof and later leaving with a bag filled with supplies. The warehouse was reported burglarized that same day.
The CCTV footage played a central evidentiary role, as it documented both the unlawful entry and the removal of goods. Confronted with this evidence, Mohamed Adam pleaded guilty in court. He was subsequently sentenced to 12 months in prison or given the option to pay a fine.
This case further illustrates how surveillance footage can provide clear, time-stamped documentation of movements and actions, significantly strengthening a prosecution's case.
Unfortunately, there are no court documents available online as Ghana rarely publish it.
Ahmed Zorduk
In 2023, in Peterborough, Ahmed Zorduk was recorded by city-centre CCTV cameras distributing wraps of Class A drugs, including cocaine and heroin. A CCTV operator monitoring the live feed observed the exchanges and alerted the police immediately.
Officers were dispatched to the area, tracked Zorduk, and stopped him. Upon search, they found drugs and cash in his possession. Confronted with both the live-observed footage and the physical evidence recovered at the time of arrest, Zorduk pleaded guilty. He was sentenced to one year and eight months in prison.

The key point illustrated by this case is that CCTV systems are not only passive recording tools. In many urban areas, they are actively monitored in real time. Operators can identify suspicious behavior, observe what individuals appear to be carrying or exchanging, and coordinate directly with law enforcement. This significantly reduces response time and increases the likelihood of interception when illegal goods are involved and it shows that what you carry can be identified from distance.
Once again, the court documents aren't available as UK Crown Court decisions are usually not published online.
Oliver Rains
In 2025, in Ely, Oliver Rains was arrested for criminal damage after carrying out graffiti on public equipment and private property. He was identified through CCTV footage that captured him in the act.
Rains later pleaded guilty and was sentenced to a 12-month community order. In addition, he was required to pay compensation for the damage caused.

This case demonstrates how CCTV can be used as direct evidentiary material in court when it captures an individual committing an offense. When footage clearly shows the act itself, it can significantly strengthen the prosecution's case.
Regarding the sentence, a community order in the UK is a form of criminal penalty that include unpaid work, supervision, or other requirements set by the court. It is a legally imposed alternative to imprisonment, but it is just disguised slavery.
The official police report is available here and it explains the usage of CCTV.
CCTV implications
For you
As the previous cases illustrate, CCTV can affect individuals in multiple ways.
The most obvious risk is being directly recorded while committing an offense. That is widely understood. However, surveillance footage can also be used in more indirect but equally impactful ways: to establish your location at a specific time, to analyze your behavior, to identify who you are meeting, to reconstruct your movements, or to contradict statements made later.

This broader evidentiary use of CCTV is often underestimated. Many people are cautious about cameras only when they believe they are engaging in “sensitive” activity. They tend to lower their guard when simply transporting items, meeting someone, or moving from one place to another. Yet those moments can be just as significant in an investigation.
Modern law enforcement agencies are highly experienced in using surveillance footage to build timelines and corroborate other evidence. As seen in earlier examples, individuals have been convicted not only because they were filmed committing an offense, but also because CCTV helped establish presence, association, or inconsistencies in their accounts.
The key takeaway is that CCTV is not merely about capturing a single incriminating act, it is a tool for comprehensive situational reconstruction.
And that's exactly what is putting you at risk. As seen in this article, everyone is a criminal, and CCTV is a tool that can be highly used to validate that statement.
CCTV systems are widely deployed across many countries, in both public and private spaces: streets, transportation hubs, shops, residential buildings, offices, and more. The practical effect is that a significant portion of daily life can potentially be recorded.
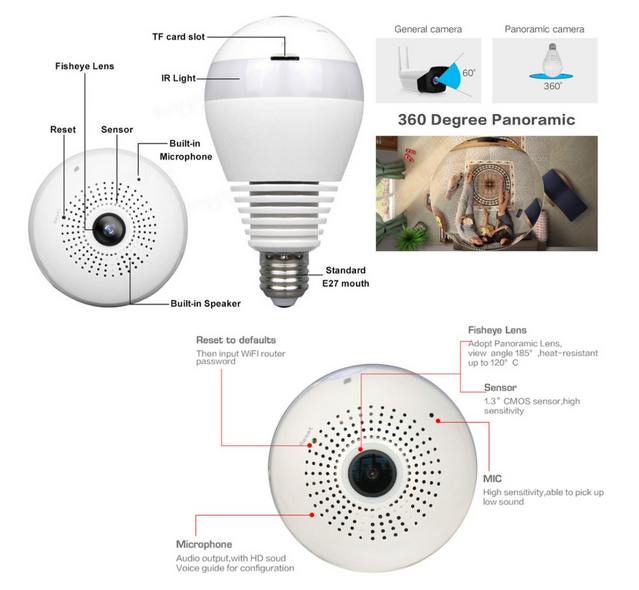
One of the main challenges is uncertainty. It is often difficult to know exactly where cameras are located, who operates them, how long footage is stored, or how it may later be used. New cameras are installed regularly, and modern devices are increasingly small, discreet, and integrated into existing infrastructure. In such an environment, awareness of how surveillance works, and how footage can be used, becomes an important part of understanding personal risk in public spaces.
For the Governments
To illustrate how CCTV is used as an investigative and prosecutorial tool, the example of the United Kingdom is particularly relevant.
In 2017, a study titled "The Value of CCTV Surveillance Cameras as an Investigative Tool: An Empirical Analysis" was published, examining the role of CCTV footage in criminal investigations. The research analyzed real case data to determine how often CCTV was available and how frequently it proved useful to investigators.
One of the most significant findings of the study concerns the proportion of cases in which CCTV footage was both available and considered valuable evidence. The study showed that CCTV was present in a substantial percentage of investigations, and when available, it was often deemed useful for identifying suspects, corroborating timelines, or supporting other forms of evidence.
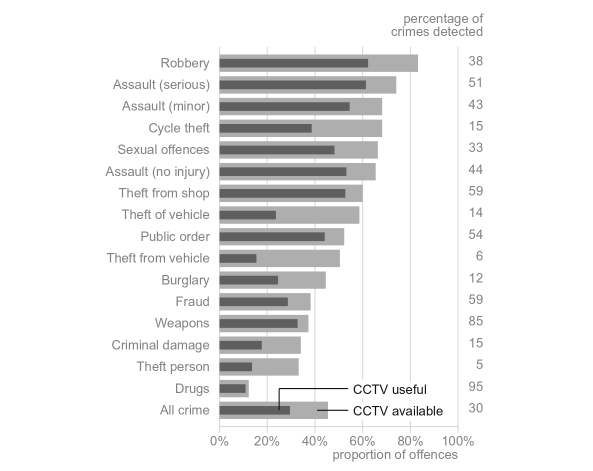
This highlights an important reality: CCTV is not merely installed for deterrence. In practice, it is regularly integrated into investigative workflows and can meaningfully influence the outcome of criminal cases.
As you may notice, drug-related offenses appear to be less frequently impacted by CCTV compared to some other types of crimes. One possible explanation is environmental selection. Individuals involved in street-level drug distribution often choose locations carefully, paying close attention to visibility, escape routes, foot traffic patterns, and potential surveillance presence.
Illicit drug markets represent a long-standing parallel economy. Over time, certain operational practices have evolved with the specific objective of reducing detection risks. These may include limiting exposure time, conducting rapid exchanges, using intermediaries, or selecting areas perceived as less monitored.
However, this does not mean that such activities are immune to surveillance. As illustrated in earlier examples, real-time monitoring, coordinated police response, and the increasing density of cameras in urban environments still present significant risks. The lower statistical impact in some datasets may reflect behavioral adaptation rather than reduced investigative capacity.

In other words, while some forms of criminal activity may attempt to adapt to surveillance-heavy environments, CCTV remains a powerful investigative tool that can be effective even when direct evidence of the act itself is not captured.
What could be done to protect yourself from CCTV
Now that you understand how widespread CCTV systems are, and that you may be under surveillance whenever you leave your home, you may be wondering how to reduce your exposure to them.
Assess your environment
First, there is no magical solution. Awareness of your surroundings is essential. Before engaging in any sensitive activity, you should assess the environment and consider whether surveillance cameras may be present. Look for visible cameras, unusual devices, or even drones.
It is important to remain realistic: detecting every surveillance device is unlikely. However, increasing your situational awareness can reduce certain risks and help you make more informed decisions about your movements and actions.
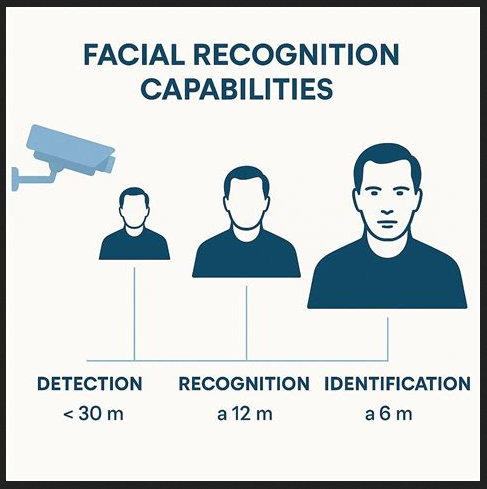
For example, it is important to understand the CCTV distances:
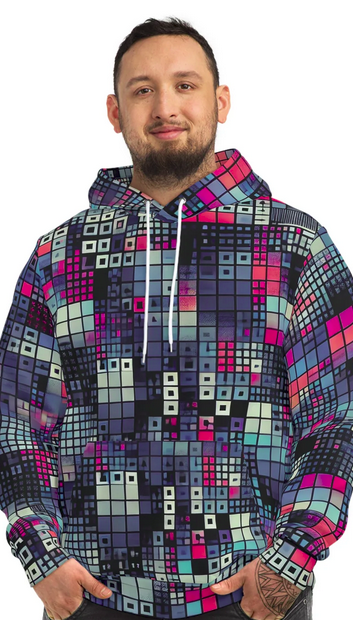
Anti-camera clothes
There is also a category of products sometimes referred to as anti-camera or anti-surveillance clothing. While it may sound like science fiction, such items do exist. They are designed with the intention of making identification by cameras more difficult.
The concept of anti-surveillance fashion is not entirely new, but its visibility and technical sophistication have increased in recent years. Some designs use patterns intended to interfere with image recognition systems, while others rely on physical obstruction of key facial features. Available items may include hoodies or scarves with disruptive prints, as well as hats and sunglasses meant to partially shield the face.
It is important to note, however, that the effectiveness of these products can vary significantly depending on lighting conditions, camera quality, angle, and the type of recognition technology in use. They may complicate identification in some contexts, but they do not guarantee anonymity.
When high-definition cameras and facial recognition software became widespread, it necessitated a more advanced approach. Designers and tech companies began experimenting with fabrics and patterns that could disrupt digital surveillance mechanisms.
People started developing fabric with complex patterns that were found to confuse facial recognition algorithms, making it difficult for cameras to identify or track people. These patterns, often resembling abstract art, are carefully designed to trick facial recognition systems into thinking it is seeing dogs, zebras, or giraffes instead.
Know how to disappear in a group
A group can be an effective way to reduce the power of facial recognition and CCTV identification. Even though CCTV systems are designed to identify individuals in crowds of hundreds, it becomes much more difficult if everyone looks the same. This approach is particularly useful during protests. If all protesters are dressed similarly and mask their faces, it becomes very challenging for CCTV to single out any one person.
We have a dedicated blog post on this topic, and I highly encourage you to read it.
However, as technology evolves and CCTV operators become increasingly trained and experienced, simply wearing the same clothes as others is not always enough to blend into a crowd. Body shape, posture, behavior, and entry or exit routes can still contribute to identification.
For this reason, effective anonymity is not limited to concealing the face. It also involves being aware of how you move, how you behave, and how predictable your patterns are. Surveillance systems may analyze gait, gestures, and other distinguishing characteristics in addition to facial features.
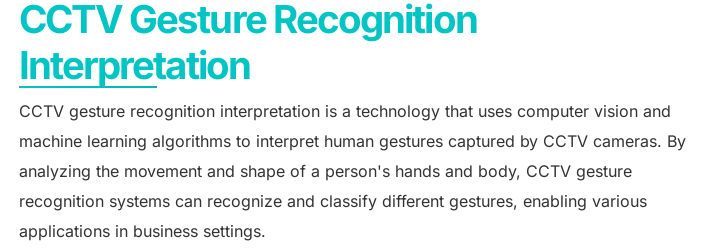
In short, it is not only a matter of hiding your face, but of understanding that identification can rely on multiple factors beyond appearance alone.
Assess the risks
When engaging in sensitive activities, some people believe it is necessary to fully control their environment. In practice, however, there are very few places where you can realistically ensure the absence of surveillance. Your home may seem like one of them, provided you are mindful of connected devices and external access points, and perhaps certain private spaces you know thoroughly and that are not accessible to others.
It might be tempting to assume that remote locations, such as forests or abandoned buildings, are inherently safe. But can you be absolutely certain there is no surveillance present? No drones, no hidden cameras, no prior monitoring? In many cases, it is difficult, if not impossible, to guarantee complete isolation from observation.
The broader point is that perceived isolation does not automatically equal security. Overconfidence in a location can create vulnerabilities. In some situations, others may anticipate movements or monitor areas in advance. Ultimately, there is rarely such a thing as a perfectly secure environment, only varying levels of risk.
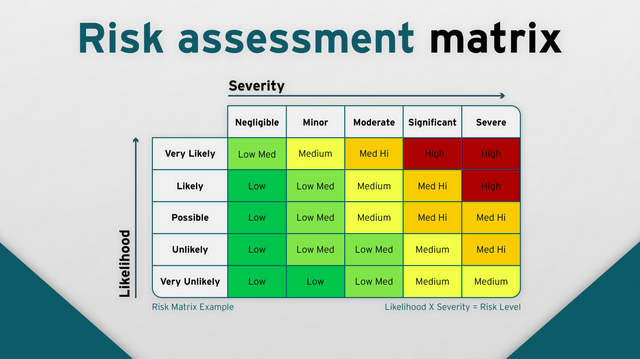
If you have no choice but to carry out a sensitive activity in an uncontrolled space, you must first understand and evaluate the risks involved.
What are the chances that you are under targeted surveillance? What legal consequences could you face if something goes wrong? Are you planning to meet someone, and is that person truly trustworthy? Could you be unexpectedly observed by a passerby or recorded indirectly?
These are essential questions that should be carefully considered before taking any action. Risk assessment is a core component of operational security (OPSEC) and should guide decision-making. Acting without evaluating potential exposure, legal implications, and environmental variables significantly increases vulnerability.
In short, informed choices require a clear understanding of both the technical and human risks involved.
Conclusion
As you can see, avoiding CCTV entirely is extremely difficult. Moreover, CCTV is not only used to catch someone in the act: it is also widely used to collect contextual elements that can later be used as evidence.
That is why applying the principles discussed in this blog post is important if your goal is to minimize risk. Extra caution is necessary when carrying out sensitive activities outside controlled environments.
Governments and law enforcement agencies have developed significant capabilities in large-scale surveillance, and any uncontrolled aspect of an environment can represent a potential vulnerability. Even indirect exposure can contribute to an investigation and, ultimately, to legal consequences.
Suggest changes
Crabmeat 2026-02-25
Donate XMR to the author:
89aWkJ8yabjWTDYcHYhS3ZCrNZiwurptzRZsEpuBLFpJgUfAK2aj74CPDSNZDRnRqeKNGTgrsi9LwGJiaQBQP4Yg5YtJw2U



